License Key Blur Pc Link
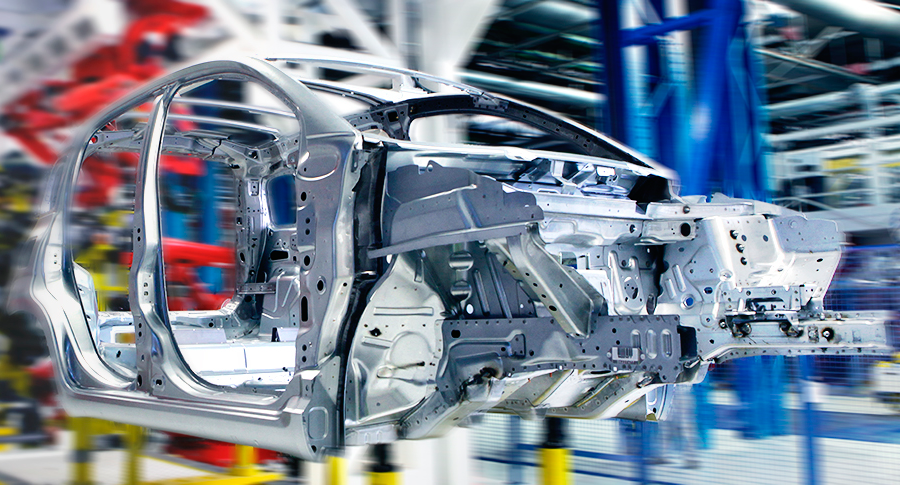
Model and Analyze Every Aspect of Your Manufacturing Processes
Arena Simulation is a product of Rockwell Automation
Arena Simulation is a product of Rockwell Automation
Arena is a discrete event simulation and automation software: it enables manufacturing organizations to increase throughput, identify process bottlenecks, improve logistics and evaluate potential process changes.


Evaluate potential alternatives to determine the best approach to optimizing performance.
Understand system performance based on key metrics such as costs, throughput, cycle times, equipment utilization and resource availability.
Reduce risk through rigorous simulation and testing of process changes before committing significant capital or resource expenditures.
Determine the impact of uncertainty and variability on system performance.
Visualize results with 2D and 3D animation

Send your technical questions to our experts!
Connect you with an EnginSoft expert who can provide a reliable answer to your technical question or recommend a
proven solution.
But why is blurring a string of letters and numbers so important? And is blurring enough to protect you? Here is everything you need to know about keeping your software licenses safe on PC. Before understanding the blur, you must understand the value of what lies beneath.
Store your actual license keys in a password manager (like Bitwarden or 1Password), not on a screenshot folder on your desktop. Your future self will thank you.
Advanced image editing software and AI tools can sometimes "unblur" text if the blur is light or applied inconsistently. Furthermore, if you use a simple black highlighter box, tech-savvy thieves can sometimes adjust the image's contrast or levels to read the text underneath. You can find countless "fail" compilings online where a tech reviewer blurred their key, but the reflection in their glasses or the metal side of their PC case revealed the key clearly. Best Practices: Beyond the Blur If you need to share a screenshot of your software activation screen, do not rely solely on the blur tool. Follow these professional-grade security steps: 1. The Solid Box Method (Safest) Do not use a blur filter. Instead, draw a solid, opaque rectangle over the license key. Ensure the color matches the background so no text data remains in the image file. Once it is covered by a solid color, the data is gone for good. 2. Crop It Out If the key is in a corner of the screen, simply crop the image. Remove the section containing the key entirely. 3. Use a Burner Key (For Tutorials) If you are creating a tutorial demonstrating how to enter a key, use a fake, invalid key (e.g., 11111-11111-11111-11111 ). Explain to your audience that this is not a real key. Never show a valid, purchasable key on stream. 4. Check Your Surroundings Before taking a screenshot or photo, check your desk. Do you have a sticky note with your password? Is your license card sitting next to the keyboard? Physical reflections are the number one cause of leaked keys. The Legal Side: DRM and Anti-Piracy Software companies are aware of the "blur culture." In fact, many modern applications use digital locks (DRM) that tie the key to your specific hardware (Motherboard ID, Hard Drive serial). license key blur pc
When you share your screen (via screenshot, streaming, or even a photo taken by a smartphone), you are broadcasting that key to the entire internet. Within minutes, bots and malicious actors can scan that image, extract the text using Optical Character Recognition (OCR), and use or sell the key.
However, even with DRM, a stolen key can be used by a hacker to generate new "offline activation" tokens. This is why companies like Microsoft have moved toward digital licenses tied to your email address rather than visible keys. When you see a blurred license key online, recognize it as a sign of a responsible PC user. That pixelated mess represents a $20, $100, or $500 piece of software that someone paid for. But why is blurring a string of letters
If you are sharing your own screen, remember: Never expose your keys, and always treat your software licenses like the valuables they are.
Even if you trust your audience, you cannot control who reposts the image. A single unblurred screenshot on a public forum can invalidate a $200 software license instantly. Here is the uncomfortable truth: Standard Gaussian blur is not foolproof. Before understanding the blur, you must understand the
If you have ever watched a tech tutorial on YouTube, seen a screenshot of a software activation window, or watched a streamer set up new PC software, you have noticed a common visual trend: a smudged, pixelated, or blacked-out rectangle where the license key should be.

CASE STUDY
This detailed technical case study describes how the students arrived at a supersonic aircraft drone prototype using MATLAB and modeFRONTIER in order to reduce the time and costs of numerical and wind-tunnel testing.
automotive modefrontier optimization
CASE STUDY
In this case study, EnginSoft engineers explain how they used modeFRONTIER to assist Comau, a Fiat Chrysler subsidiary, to optimize their approach to the preliminary design of production systems for automotive manufacturing system RFQs.
automotive optimization rail-transport modefrontier SIMUL8 iphysics industry4
CASE STUDY
A fascinating article on the origin, history, and evolution of roller coasters from their earliest prototypes in Russia in the 16th century on the banks of the Neva River of St. Petersburg, and then dives into detail on how numerical simulation of roller coasters works to ensure their success both as entertainment and from a safety perspective for users and operators.
mechanics civil-engineering construction optimization